Bitcoin Fog founder arrested with help of Google, Twitter, and Microsoft

Bitcoin mixer Bitcoin Fog — a service almost as old as the protocol itself — has been put to rest with the help of tech giants Microsoft, Google, and Twitter.
The IRS’ Criminal Investigation (CI) unit charged Bitcoin Fog’s Roman Sterlingov in Los Angeles on Tuesday with money laundering and transmission without a license.
The arrest of Sterlingov, a Russian and Swedish dual-citizen, came after a joint investigation by the Federal Bureau of Investigation and IRS-CI that started in 2019.
Authorities describe the platform as a “darknet money laundering service” advertised on the clearnet.
Bitcoin Fog tried to make transactions anonymous
Bitcoin Fog accepted Bitcoin and co-mingled it with others for a 2-2.5% fee, rendering it difficult to track their provenance.
But the site brazenly maintained a Twitter account for marketing purposes. According to the affidavit, Bitcoin Fog’s account shared articles detailing the necessity of hiding Bitcoin transaction histories from law enforcement.
Bitcoin Fog even once boasted that alternatives not utilizing privacy-based web browser Tor were doomed to fail.
- Bitcoin Fog was launched in October 2011 and was operational until Sterlingov’s arrest.
- Over 1.2 million BTC allegedly flowed through it — over 6% of all Bitcoin in circulation.
- Police valued the Bitcoin it washed at $336 million. At today’s prices, the full sum is worth over $65 billion.
Authorities found Bitcoin Fog mostly handled Bitcoin from darknet markets like Silk Road, Agora, Evolution, and AlphaBay.
It started with a suspect email request
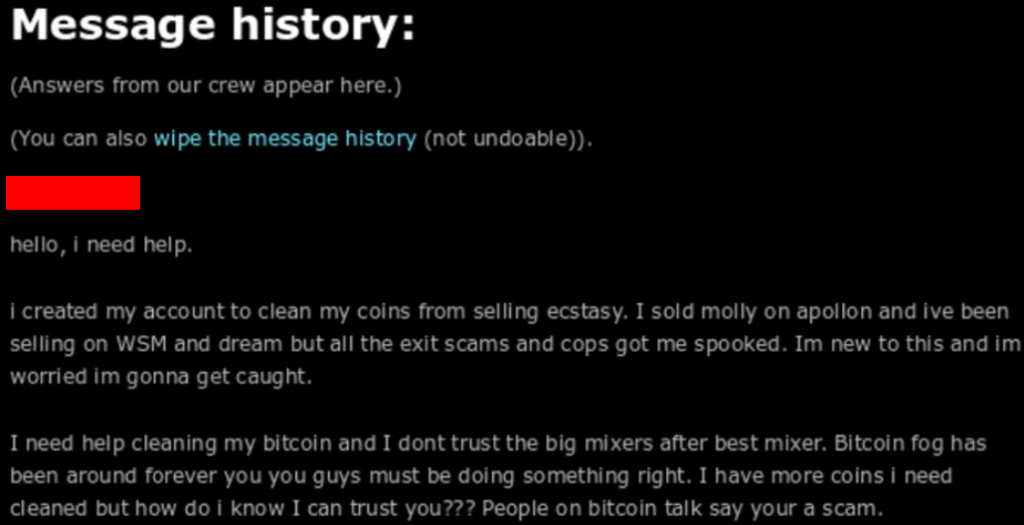
As for how the Feds caught Sterlingov: special agent Devon Beckett sent a personal message asking for proof he could trust Bitcoin Fog with laundering BTC obtained by selling ecstasy on the darknet.
Sterlingov didn’t respond. However, Beckett was still able to deposit 0.011 BTC without any issues.
With the “illicit” Bitcoin accepted, police linked the service to Sterlingov by obtaining financial, ISP, and email records.
Police noted Sterlingov has repeatedly used the pseudonym “Akemashite Omedotou” and the email address “[email protected].”
- Using that address, Omedetou registered with popular forum BitcoinTalk, where they announced Bitcoin Fog’s launch.
- The same email address registered Bitcoin Fog’s Twitter account.
- WHOIS information for the service’s clearnet site listed Omedetou and the email address.
With this knowledge (along with phone and crypto exchange data), authorities tied Sterlingov to a number of exchanges used in Bitcoin Fog’s mixing system.
Blockchain analytics showed Sterlingov controlled many of the accounts leveraged by the platform to wash crypto.
Google came through for the Feds
The Big G gave the police access to Sterlingov’s Drive accounts after they obtained a federal search warrant.
One of Sterlingov’s Google Drive folders housed a Russian language document with a title that translated to “Putting Money.”
The doc contained notes on how to layer funds and apparently showed how Sterlingov created Bitcoin Fog without giving away too much personal information.
“The steps outlined in the document match the steps that Sterlingov took to pay for the domain www.bitcoinfog.com,” wrote Beckett.

[Read more: Dark web giant Joker’s Stash just ‘retired’ with $1B in Bitcoin]
At his time of arrest, the IRS valued Sterlingov’s known personal Bitcoin stash at roughly $70 million. However, that doesn’t account for his other potential assets yet to be determined.
Bitcoin Fog’s clearnet site can still be accessed but the Feds seemingly have shut the Tor site down. Protos has reached out to the IRS for comment.
