Darknet market directory hacked with fake court order to steal Bitcoin

Hackers recently took control of a darknet market directory to phish Bitcoin from unsuspecting drug buyers, reports Vice.
The attack on dark.fail — which ran for four days — meant anyone using darknet markets linked by the site may have lost crypto and other sensitive data.
An unknown individual acquired dark.fail on April 28 after they served fake court orders to transfer the site’s ownership to a new admin.
- Privacy-centric Njalla (co-founded by Pirate Bay’s Peter Sunde in 2017) manages dark.fail.
- Njalla is middleware — buying domains for users to protect their anonymity.
- Internet staple Tucows sold dark.fail to Njalla (via Tucows’ Hover).

Dark.fail hacker sure knows a lot about court orders
In a series of tweets, Sunde explained how Tucows fell victim to social engineering.
Tucows received an order from the district court of Cologne, Germany to demand ownership of three domains — two registered with Njalla and one through Hover.
Njalla and Tucows’ Hover complied with the fake requests and transferred dark.fail to the attacker’s Namecheap registration.
“The fake court order also included a gag order, to not inform the registrant that this was happening,” said Sunde.
“This means that neither Njalla nor Hover was informed about what was going to happen and had no possibility of stopping the transfer,” he added.
Once the transfer had taken place, the attacker altered all links dark.fail to phish passwords, usernames, and other vulnerable data.
Making digital cash by posing as darknet markets
Though Njalla and Hover were apparently quick to respond to the phishing attack, Sunde claimed Namecheap refused to transfer the rights back for four days.
Darknet markets generally accept Bitcoin. So, during the attack, fraudsters may have fooled dark.fail users into sending Bitcoin to addresses under their control.
Sunde noted the hackers were “most likely making a lot of money and collecting sensitive user data.”
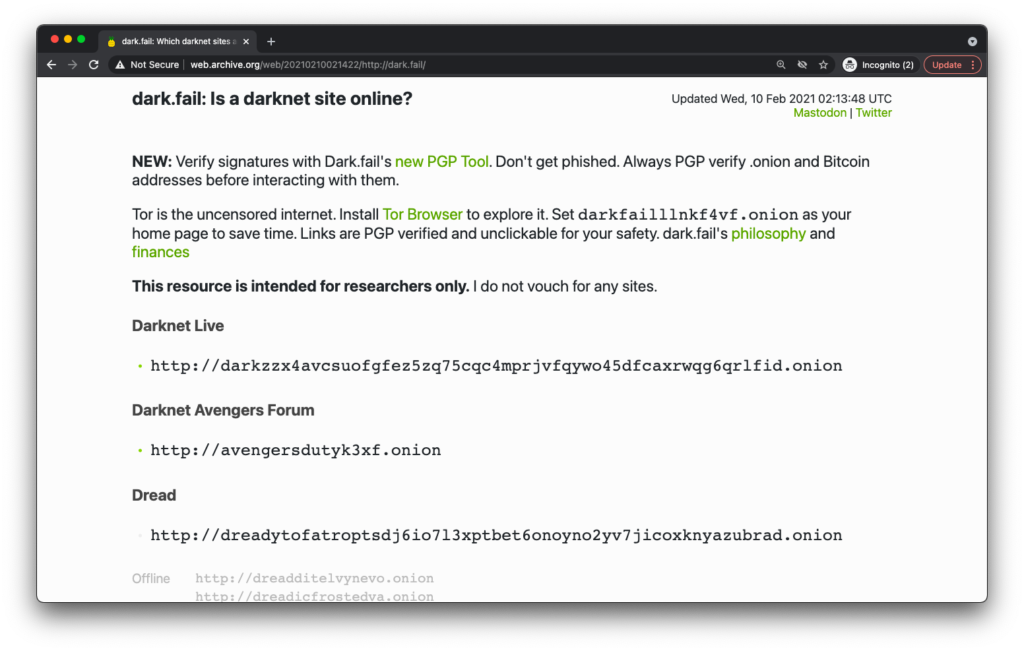
The onion version of dark.fail — accessible through Tor — remains operational. It’s unclear how many individuals had data compromised in the attack.
It’s also unknown who could pull off such a targeted ruse.
Sunde reasoned it was someone with insight into how domain hosts handle court requests.
[Read more: A history of Bitcoin Fog, the crypto mixer that washed 6% of BTC’s supply]
“The court order makes me believe that the attacker is very well versed in how these court orders usually look, and have directed it extremely well within Tucows,” said Sunde.
